Article At A Glance
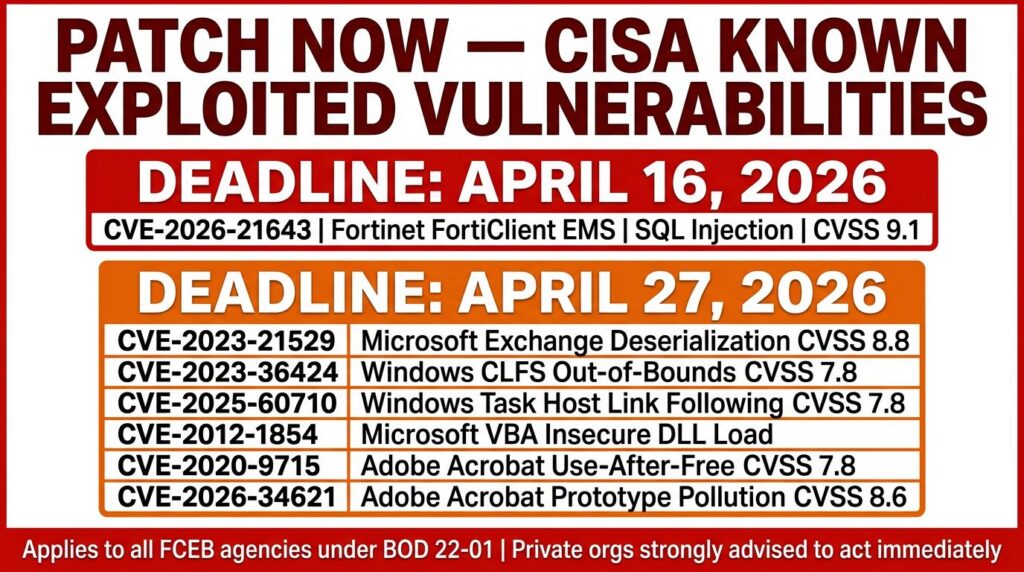
- CISA added six actively exploited vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog on April 13, 2026, spanning Fortinet, Microsoft, and Adobe products.
- Two of the six flaws are over a decade old, proving that unpatched legacy software remains one of the most dangerous attack surfaces in any environment.
- Federal agencies are bound by mandatory remediation deadlines, but private organizations should treat these listings as urgent action items — not optional guidance.
- The six CVEs cover a wide range of attack techniques including SQL injection, prototype pollution, use-after-free, and deserialization of untrusted data.
- One of the most critical flaws targets Microsoft Exchange Server — keep reading to understand exactly how attackers weaponize it and what you need to do immediately.
If your organization runs Fortinet, Microsoft, or Adobe software, you need to stop and read this now.
On April 13, 2026, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) updated its Known Exploited Vulnerabilities (KEV) catalog with six newly confirmed flaws — all of them being actively weaponized by attackers in real-world environments. This is not theoretical risk. These are confirmed, in-the-wild exploits hitting enterprise systems right now. SecureReading, a cybersecurity intelligence resource that tracks active threat campaigns and CISA catalog updates, flagged this development immediately as a high-priority threat for both public and private sector organizations.
What makes this update especially alarming is the mix of old and new. One CVE dates back to 2012, another to 2020 — and both are still being successfully exploited today. That tells you something critical: attackers do not need cutting-edge zero-days when organizations leave years-old vulnerabilities unpatched.
6 Flaws. 3 Vendors. Active Exploitation Right Now.
Three of the most widely deployed technology vendors in the enterprise world — Microsoft, Adobe, and Fortinet — are all represented in this single KEV update. That is not a coincidence. These platforms sit at the core of business infrastructure globally, which is exactly what makes them such high-value targets. When a flaw is confirmed in any one of these ecosystems, the blast radius is enormous. Recently, an emergency patch for FortiClient EMS was released due to active exploitation.
What CISA’s KEV Catalog Addition Actually Means
CISA’s Known Exploited Vulnerabilities catalog is not a wish list or a theoretical risk register. It is a curated database of security flaws that have been confirmed as actively exploited in the wild. Every entry requires verified evidence of exploitation — not just proof-of-concept research. When CISA adds a CVE to this list, it simultaneously issues a directive requiring all U.S. federal civilian executive branch agencies to remediate the flaw by a specific deadline. For private organizations, there is no legal mandate, but ignoring these listings is a serious risk management failure.
Why These Flaws Were Flagged Over Thousands of Others
There are over 200,000 CVEs in existence. CISA’s KEV catalog contains a fraction of those — because most vulnerabilities, while real, never get weaponized at scale. The ones that make the catalog are the ones that threat actors are actively integrating into attack chains, ransomware deployments, and espionage campaigns. These six CVEs passed that threshold. They were not added because they have high CVSS scores on paper. They were added because exploitation evidence was confirmed.
The 6 Exploited Vulnerabilities, Broken Down
Here is a direct breakdown of each flaw added in this update, what it affects, and why it matters for your security posture. For instance, the emergency patch for FortiClient EMS highlights the importance of addressing these vulnerabilities swiftly to protect your systems from potential threats.
CVE-2012-1854: Microsoft Visual Basic for Applications Insecure Library Loading
This vulnerability is over thirteen years old and it is still being exploited. CVE-2012-1854 affects Microsoft Visual Basic for Applications (VBA) and involves insecure DLL loading — a technique where an attacker places a malicious library file in a location that a vulnerable application loads automatically. When a user opens a crafted document or triggers the VBA runtime, the malicious DLL executes with the privileges of the running process. The fact that this flaw is still seeing active exploitation in 2026 is a direct indictment of patch management hygiene across many organizations.
CVE-2020-9715: Adobe Acrobat Use-After-Free
CVE-2020-9715 is a use-after-free vulnerability in Adobe Acrobat. Use-after-free bugs occur when a program continues to use a memory pointer after the memory it references has been freed, allowing an attacker to inject malicious data into that memory space and redirect program execution. In Acrobat’s case, this can be triggered through a specially crafted PDF file — one of the most common document formats in enterprise environments. A user simply opens the file and code executes. No additional interaction required.
CVE-2023-21529: Microsoft Exchange Server Deserialization of Untrusted Data
CVE-2023-21529 targets Microsoft Exchange Server through a deserialization of untrusted data vulnerability. Deserialization flaws are particularly dangerous because they allow attackers to send malicious serialized objects to a server, which then processes them as legitimate data. In Exchange’s case, this can result in remote code execution — meaning an attacker can run arbitrary commands on your mail server without any user interaction on the target side.
Exchange Server has been one of the most persistently targeted enterprise products over the last several years. Nation-state actors, ransomware groups, and financially motivated criminal organizations have all built attack tooling around Exchange vulnerabilities. CVE-2023-21529 fits squarely into that pattern.
The attack surface here is broad. Any organization running an on-premises Exchange Server deployment that has not applied the relevant patch is exposed. This includes environments that believe they are protected because they run perimeter firewalls — Exchange exploitation does not always require external network access when internal threat vectors are considered.
- Affected product: Microsoft Exchange Server
- Vulnerability type: Deserialization of untrusted data
- Potential impact: Remote code execution
- User interaction required: None (server-side exploitation)
- Actively exploited: Confirmed by CISA
CVE-2023-36424: Microsoft Windows Out-of-Bounds Read
CVE-2023-36424 is an out-of-bounds read vulnerability in Microsoft Windows. This class of bug allows an attacker to read memory beyond the boundaries of an allocated buffer, which can leak sensitive information from system memory or be chained with other vulnerabilities to achieve privilege escalation or code execution.
Out-of-bounds read vulnerabilities are frequently used as a stepping stone in multi-stage attacks. An attacker compromises an initial entry point, uses the memory leak to gather information about the system’s memory layout, and then uses that intelligence to bypass protections like ASLR (Address Space Layout Randomization) before executing a more destructive payload.
- Often used as a precursor in chained exploit sequences
- Can leak kernel memory contents, including credentials or encryption keys
- Particularly dangerous in environments where lateral movement is possible after initial access
CVE-2026-21643: Fortinet SQL Injection
CVE-2026-21643 is a SQL injection vulnerability affecting Fortinet products. SQL injection remains one of the most consistently weaponized vulnerability classes in existence because it directly targets the database layer of an application. A successful exploit allows an attacker to manipulate database queries, extract sensitive data, modify records, or in some configurations achieve command execution on the underlying host.
Fortinet devices are widely deployed at the network perimeter — firewalls, VPN gateways, and network access control systems. A SQL injection flaw in this context does not just threaten the device itself. It threatens the entire network boundary that device is responsible for protecting.
CVE-2026-34621: Adobe Acrobat and Reader Prototype Pollution
CVE-2026-34621 is a prototype pollution vulnerability in Adobe Acrobat and Reader. Prototype pollution is a JavaScript-based attack class where an attacker manipulates the prototype chain of an object, injecting properties that propagate across the application’s object hierarchy. In document rendering contexts like Acrobat, this can lead to arbitrary code execution when a malicious PDF is opened — making it a potent phishing and drive-by attack vector.
Why Attackers Target These Three Vendors
Microsoft, Adobe, and Fortinet are not random targets. They represent three of the most deeply embedded technology layers in enterprise infrastructure worldwide — productivity and operating systems, document workflows, and network security. When attackers invest in building exploits for these platforms, the return on that investment is enormous because the potential victim pool is massive. This is evident from recent incidents like the European Commission cloud systems cyberattack, which highlights the vulnerabilities in widely used systems.
There is also a compounding factor: organizations that run these platforms at scale often struggle to patch them quickly. Complex dependencies, uptime requirements, and change management processes create windows of exposure that attackers have learned to exploit systematically.
Fortinet’s Role at the Network Perimeter Makes It a Prime Target
Fortinet products sit at the edge of networks — handling firewall rules, VPN authentication, and network access control for millions of organizations globally. That positioning makes a successful exploit extraordinarily valuable. An attacker who compromises a Fortinet device does not just gain access to one system. They gain a foothold at the boundary of an entire network, with potential visibility into all traffic crossing that boundary.
Ransomware groups and nation-state actors have both demonstrated a pattern of specifically hunting for vulnerable Fortinet devices exposed to the internet. Initial access brokers — criminal actors who sell network access to other threat groups — regularly list compromised Fortinet appliances as their entry point. CVE-2026-21643’s SQL injection class fits exactly the kind of flaw these actors actively scan for.
Microsoft’s Ecosystem Scale Means Exploits Travel Fast
Microsoft’s dominance in enterprise computing means that a single exploitable flaw can theoretically affect hundreds of millions of systems simultaneously. Windows, Exchange Server, and the VBA runtime are deployed in virtually every industry sector — finance, healthcare, government, critical infrastructure, and small business alike. That universality is precisely what makes Microsoft vulnerabilities so attractive to attackers.
The three Microsoft CVEs in this update — CVE-2012-1854, CVE-2023-21529, and CVE-2023-36424 — each target different layers of the Microsoft stack. One hits the VBA runtime embedded in Office documents, one hits Exchange Server’s mail processing engine, and one hits Windows itself. Together, they represent a multi-vector threat that can enter an environment through email, document, or direct network exploitation.
Real-World Attack Chain Example: An attacker sends a phishing email with a malicious PDF attachment (CVE-2026-34621 in Adobe Acrobat). Once opened, it executes code that performs reconnaissance using CVE-2023-36424’s memory leak capability. The attacker then pivots to the Exchange Server and exploits CVE-2023-21529 for persistent remote access. Three CVEs. One attack chain. Complete network compromise.
Adobe’s Widespread Enterprise Use Creates Broad Attack Surface
Adobe Acrobat and Reader are installed on an estimated hundreds of millions of endpoints globally. In enterprise environments, PDF is the default format for contracts, invoices, reports, and inter-organizational communication. That ubiquity means malicious PDFs are one of the most reliable delivery mechanisms in an attacker’s arsenal — users are conditioned to open them without suspicion.
Both Adobe CVEs in this update — CVE-2020-9715 and CVE-2026-34621 — are triggerable through document opening. No macros need to be enabled. No special permissions are required. The user opens what looks like a normal PDF and the exploit fires silently in the background. This makes Adobe flaws particularly effective in phishing campaigns targeting employees who handle high volumes of document-based communication.
The six-year gap between CVE-2020-9715 and its confirmed active exploitation status in 2026 also reveals something important about attacker behavior. Threat actors maintain libraries of working exploits for unpatched systems and deploy them opportunistically. An organization that never patched a 2020 Adobe flaw is just as exposed today as it was when the CVE was first published.
What “Actively Exploited” Really Means for Your Organization
The phrase “actively exploited” carries a very specific meaning in the context of CISA’s KEV catalog — and understanding that distinction is critical for prioritizing your response correctly.
The Difference Between a CVE Score and Real-World Threat Level
The Common Vulnerability Scoring System (CVSS) assigns a numerical severity score to vulnerabilities based on factors like attack complexity, privileges required, and potential impact. It is a useful baseline. But a high CVSS score does not automatically mean a vulnerability is being actively exploited, and a moderate CVSS score does not mean a flaw is safe to deprioritize. CVSS measures theoretical severity. The KEV catalog measures actual danger.
CVE-2023-36424, the Windows out-of-bounds read flaw, may score lower on CVSS than a critical remote code execution vulnerability — but its confirmed active exploitation and its role as a chaining component in multi-stage attacks makes it operationally more dangerous than many higher-scored CVEs that exist only in proof-of-concept form. Patch prioritization based solely on CVSS scores is a flawed strategy that leaves real gaps in your defense.
How CISA Confirms Active Exploitation Before Listing a Flaw
CISA does not add vulnerabilities to the KEV catalog based on vendor advisories or researcher speculation alone. The agency requires credible evidence of active exploitation — typically sourced from threat intelligence reporting, incident response data, government sensor networks, or direct reporting from affected organizations and security vendors.
This vetting process means that by the time a CVE appears in the KEV catalog, exploitation has already been occurring — potentially for weeks or months before the listing. The catalog addition is not an early warning. It is confirmation that attackers are already in the field using this weapon. Your response timeline is not measured in weeks. It is measured in hours.
For the six CVEs added on April 13, 2026, confirmed exploitation evidence existed across multiple sources before CISA made the formal addition. Organizations waiting for the catalog listing to begin their response were already behind.
What You Need to Do Right Now
This is not a situation where you schedule a review for next quarter’s patch cycle. These are confirmed active exploits targeting software you almost certainly run. Here is the prioritized action sequence.
1. Audit Your Exposure Across All Three Vendors Immediately
Before you can patch anything, you need to know exactly which versions of Fortinet, Microsoft, and Adobe software are running across your environment. Run a full asset inventory against all six CVEs using your vulnerability management platform. If you do not have one, use CISA’s free Cyber Hygiene Vulnerability Scanning service as a starting point. Document every instance of affected software — including systems that may not be on your primary patch schedule, such as legacy servers, branch office equipment, or contractor-managed endpoints.
2. Apply Available Patches Before the Federal Remediation Deadline
Each CVE added to the KEV catalog comes with a federally mandated remediation deadline for U.S. government agencies — typically ranging from two to four weeks depending on severity and exploitation context. While private organizations are not legally bound by these deadlines, they represent a practical and well-reasoned remediation timeline. Vendor patches are available for all six CVEs in this update. Access them directly through Microsoft’s Security Update Guide, Adobe’s Security Bulletins page, and Fortinet’s Product Security Incident Response Team (PSIRT) advisories. Do not download patches from third-party sources.
3. Isolate Unpatched Systems That Cannot Be Updated Immediately
Not every system can be patched instantly. Legacy servers with hard dependencies, operational technology environments, and systems managed by third-party vendors may require additional lead time before a patch can be safely applied. In those cases, isolation is your next best defense. Segment unpatched systems behind additional firewall rules, restrict inbound and outbound communication to only what is operationally necessary, and remove internet-facing exposure wherever possible.
For Fortinet devices specifically, if CVE-2026-21643 cannot be patched immediately, restrict management interface access to trusted IP ranges only and disable any unnecessary external-facing services on the affected appliance. For unpatched Exchange Servers vulnerable to CVE-2023-21529, consider placing the server behind an application-layer gateway that can inspect and block malformed serialized data before it reaches the Exchange service.
4. Monitor for Indicators of Compromise Tied to These CVEs
Patching closes the door. Monitoring tells you whether someone already walked through it. Pull threat intelligence indicators of compromise (IOCs) associated with each of these six CVEs from CISA’s KEV catalog entries, your threat intelligence platform, and vendor-specific security advisories. Configure your SIEM to alert on process injection events, anomalous DLL loading sequences, unexpected Exchange PowerShell activity, and unusual outbound connections from Fortinet management interfaces. If you do not have a SIEM, at minimum enable enhanced logging on all affected systems and review logs daily until patches are confirmed applied.
5. Report Active Exploitation Evidence Directly to CISA
If your organization detects active exploitation of any of these six vulnerabilities in your environment, report it directly to CISA at their official reporting portal. This is not just civic responsibility — it directly contributes to the threat intelligence pool that CISA uses to update the KEV catalog, issue emergency directives, and warn other organizations before they are hit. Timely reporting of confirmed exploitation can protect thousands of other organizations that may not yet know they are exposed.
Old CVEs Still Being Exploited Is the Real Warning Here
CVE-2012-1854 was published fourteen years ago. CVE-2020-9715 was published six years ago. Both are confirmed as actively exploited in 2026. That single fact should reshape how every organization thinks about vulnerability management.
The cybersecurity industry has a persistent fixation on new vulnerabilities — zero-days, freshly published CVEs, and the latest vendor advisories dominate the headlines. But the data tells a different story. Attackers are extraordinarily patient and pragmatic. They maintain working exploit libraries for vulnerabilities that were never patched across large portions of their target population, and they deploy those exploits continuously until the opportunity disappears.
This means your threat surface is not just defined by what was published last month. It is defined by every unpatched vulnerability in your environment regardless of when it was discovered. An organization that patched everything released in 2025 but never addressed a 2020 Adobe flaw has a 2020-sized hole in its defenses that attackers are actively scanning for and exploiting right now.
The solution is not just faster patching of new CVEs. It is systematic backfill of historical vulnerabilities using the KEV catalog as a prioritization tool. Every entry in that catalog represents a confirmed, weaponized flaw. Working backward through the list and closing those gaps is one of the highest-return security investments any organization can make.
| CVE | Vendor | Year Published | Vulnerability Type | Potential Impact |
|---|---|---|---|---|
| CVE-2012-1854 | Microsoft | 2012 | Insecure Library Loading | Arbitrary code execution via malicious DLL |
| CVE-2020-9715 | Adobe Acrobat | 2020 | Use-After-Free | Code execution via crafted PDF |
| CVE-2023-21529 | Microsoft Exchange | 2023 | Deserialization of Untrusted Data | Remote code execution, no user interaction |
| CVE-2023-36424 | Microsoft Windows | 2023 | Out-of-Bounds Read | Memory leak, privilege escalation chain |
| CVE-2026-21643 | Fortinet | 2026 | SQL Injection | Database access, potential host command execution |
| CVE-2026-34621 | Adobe Acrobat & Reader | 2026 | Prototype Pollution | Arbitrary code execution via malicious PDF |
Frequently Asked Questions
These are the most common questions organizations ask when a CISA KEV update like this one drops — answered directly.
What is CISA’s Known Exploited Vulnerabilities Catalog?
The Known Exploited Vulnerabilities catalog is a continuously updated database maintained by the U.S. Cybersecurity and Infrastructure Security Agency that lists security flaws confirmed as actively exploited in real-world attacks. Unlike general CVE databases that track all disclosed vulnerabilities regardless of exploitation status, the KEV catalog is specifically curated to highlight flaws that have been verified as weapons in active attack campaigns.
Each entry includes the CVE identifier, the affected vendor and product, a short description of the vulnerability, and a required remediation date for U.S. federal civilian executive branch agencies. The catalog is publicly available and serves as one of the most reliable prioritization signals for security teams managing large vulnerability backlogs across any sector.
Are Private Organizations Required to Patch These Vulnerabilities?
No. CISA’s Binding Operational Directive 22-01, which established the mandatory patching requirement tied to the KEV catalog, applies specifically to U.S. federal civilian executive branch agencies. Private sector organizations, state and local governments, and international entities are not legally required to comply with KEV remediation deadlines.
However, treating these listings as optional is a serious risk management error. Cyber insurance providers are increasingly referencing KEV catalog status in coverage decisions and claim assessments. Regulatory frameworks including HIPAA, PCI-DSS, and CMMC have provisions that effectively require timely remediation of known exploited vulnerabilities even where the KEV catalog is not explicitly cited. Beyond compliance, the practical reality is simple: if CISA has confirmed active exploitation, attackers are already scanning for and targeting your systems if they are unpatched.
How Quickly Do Federal Agencies Have to Remediate KEV-Listed Flaws?
Under Binding Operational Directive 22-01, federal civilian executive branch agencies are typically required to remediate KEV-listed vulnerabilities within two weeks for flaws with a prior remediation date, and within the timeframe specified in the catalog entry for newly added CVEs. CISA sets these deadlines based on the assessed exploitation severity and available remediation options.
For the six CVEs added on April 13, 2026, agencies were given specific remediation deadlines tied to each individual CVE based on its exploitation context and the complexity of available patches. Private organizations should use these federal deadlines as a practical benchmark — if the U.S. government is requiring its agencies to patch within two weeks, that timeline reflects genuine operational urgency that applies equally to any organization running the same affected software.
How Do Attackers Exploit a Flaw Like CVE-2023-21529 in Microsoft Exchange?
CVE-2023-21529 is a deserialization of untrusted data vulnerability, which means the Exchange Server can be manipulated into processing malicious serialized objects as if they were legitimate data. An attacker sends a specially crafted request to the Exchange Server — typically over the network without requiring authentication in the most severe exploitation scenarios — containing a malicious serialized payload. When Exchange processes the request, it deserializes the object, and the attacker-controlled code embedded within it executes on the server.
The resulting impact is remote code execution — meaning the attacker can run any command they choose on the Exchange Server with the privileges of the Exchange service account. From that position, attackers can exfiltrate email data, establish persistent backdoors, move laterally to other systems on the same network segment, or deploy ransomware payloads across the environment. Exchange Servers are high-value targets specifically because they sit at the center of organizational communication and are frequently granted broad internal network access to fulfill their mail routing function.
Where Can I Find Official Patches for These Six Vulnerabilities?
All patches should be sourced exclusively from official vendor channels. For Microsoft CVEs including CVE-2012-1854, CVE-2023-21529, and CVE-2023-36424, patches are available through the Microsoft Security Update Guide at microsoft.com/en-us/msrc. Search by CVE number to locate the exact security update for your affected product version. For Windows and Exchange, patches are also distributed through Windows Update and Windows Server Update Services (WSUS).
For Adobe CVEs including CVE-2020-9715 and CVE-2026-34621, patches are available through the Adobe Security Bulletins and Advisories page at helpx.adobe.com/security. Adobe also distributes updates through the Adobe Acrobat and Reader built-in update mechanism — ensure auto-update is enabled and force an immediate check rather than waiting for the scheduled update cycle.
For Fortinet’s CVE-2026-21643, patches and mitigation guidance are published through Fortinet’s Product Security Incident Response Team (PSIRT) advisories at fortiguard.fortinet.com/psirt. Fortinet also notifies registered customers of critical security updates through their support portal. If your Fortinet environment is managed by a third-party vendor or MSP, escalate immediately and confirm patching status in writing with a documented timeline.
SecureReading monitors active threat campaigns and CISA catalog updates continuously, providing organizations with the timely intelligence needed to respond to exactly these kinds of fast-moving threats before attackers find their way in.